The internet is filled with almost all sorts of threats. And if you don’t think before you click, you may end up exposing all sensitive information on your devices. You don’t want that to happen, right?
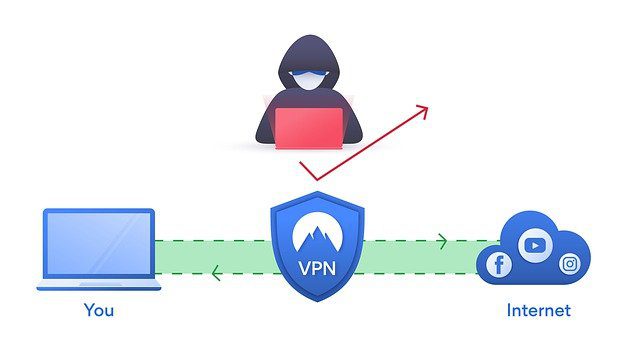
To allow users to browse the web securely, VPN services are introduced. They protect internet users and their sensitive data from prying eyes and other malicious entities. However, while VPN services are designed to protect users against hackers, they sometimes fail to do what they’re supposed to do and get attacked instead. Ironic, huh?
You may think it’s just a random scenario that came out from a creative mind, but no. It is really happening. Chinese hackers have been recently launching attacks on various VPN services all over the world. While most of these attacks target renowned VPN providers, others choose to attack smaller VPN service providers.
Even with all these attacks, VPN providers are doing their part, resolving the vulnerabilities and fixing loopholes that are being exploited by hackers. But still, these attack incidents have instilled fear and worry on many users. They are concerned whether or not the VPN service they currently use is vulnerable to these attacks.
Let’s try to address your VPN concerns through this article. In the next sections, we will investigate the recent Chinese VPN attacks, particularly how and why they happened and what has been done so far to prevent them.
Chinese VPN Attacks: Should You Be Afraid?
Last year, cybersecurity experts discussed the attacks against two major players in the industry: Pulse Secure and Fortigate. According to them, the attacks were carried out after vulnerabilities in their VPN products were known during the Black Hat USA security conference.
Manganese, also known as APT5, was believed to be at the helm of the attacks. This group is composed of hackers who use different tactics and equipment. Since their presence was known in 2007, the group has become notorious attackers of various industries in the IT sector.
In late August of 2020, APT5 began its attacks. They searched the internet for Pulse Secure and Fortigate’s VPN servers, hoping that they could exploit their vulnerabilities. And it seems that they were successful with their plans as they were able to retrieve sensitive files from the servers even without authentication. With the files that APT5 has collected, they managed to take over many vulnerable devices.
Thanks to the researchers from Devcore, the vulnerabilities were then discovered. Soon, Pulse Secure rolled out a patch. Fortigate followed thereafter.
Unfortunately, users of the concerned VPN services said they were not aware of the issue. Worse, they did not even know that a patch was available for installation. So, until now, researchers cannot tell the extent of the damage and how much data the attackers were able to collect.
Well, this is not the first case of Chinese VPN attacks. Back in 2015, an established Chinese VPN platform called Terracota managed to penetrate and attack the servers of many businesses. They stole the computer powers and bandwidth of these servers and sold them to hackers.
Can VPN Services Be Hacked?
We all know that using a VPN can protect us while surfing the web and keep our data secure. However, this level of protection that VPNs offer is futile if they can be easily hacked. So, how secure is the VPN you are using?
When gauging the level of security of VPNs, there are two major factors that we have to look into–VPN leaks and encryption.
In case you don’t know, a VPN works by directing your internet traffic through an encrypted tunnel to its server. Because of this tunnel, nobody can monitor your browsing activities, not even your internet service provider.
When you access the web with a VPN service, your identity and privacy become protected. Your communications are also kept confidential.
To connect to a VPN server, launch the VPN client first. And then, connect to your chosen server. Once the connection is successful, you can proceed with browsing the web anonymously.
But then again, how can you ensure that your VPN connection is secure? Let’s have a look at the various things that impact a VPN’s security level.
Encryption
VPN services follow a protocol to secure and encrypt private data. And most VPN service providers often allow users to choose what protocol to use. Among the most popular options are Internet Protocol Security, Point-to-Point Tunnelling Protocol, and OpenVPN.
How does VPN encryption work, you may ask. The idea is to turn readable data into something completely unreadable, called ciphertext, as it goes through the VPN tunnel. To encrypt or decrypt this data, an algorithm is defined as well. The common algorithms used by VPNs are hashing, asymmetric, and symmetric.
Hashing is basically a one-way encryption type that is irreversible. It is designed to protect the integrity of the data being transmitted. Symmetric, on the one hand, works by using one key to encrypt and decrypt information. Meanwhile, asymmetric uses two different keys to read and decipher data.
Now, how do hackers exploit a VPN’s encryption to retrieve data? There are two ways that cyber criminals do this. It’s either they steal the key or break the encryption.
Hackers may carry out cryptographic attacks to recover plain information from the encrypted data without using the key. But take note that breaking the encryption is not practical for hackers because the method consumes significant computing power and time. In most cases, it will take years to break the encryption.
Because of that, hackers prefer to steal keys to access data. It’s way easier and more efficient compared to brute force attacks.
IP and DNS Leaks
Aside from encryption, IP and DNS leaks are other loopholes that hackers use to gain access to your VPN. DNS leaks mostly happen when you connect to an unsecured DNS server, which is assigned by your ISP. In this case, your ISP can see what sites you are visiting.
IP leaks, on one hand, happen if your browser leaks your true IP address while transmitting data. Though cyber criminals cannot access your data with IP leaks, they can still see your location and get information about your identity.
Now, you have to be careful with choosing VPN providers. Some of them offer built-in protection, while others do not. To be sure, check it out yourself using websites that are meant for checking VPN leaks.
Will You Use a VPN?
Knowing that VPNs can be hacked, will you continue using them? Of course, you should. Cyber criminals are getting smarter nowadays, and they will continue looking for loopholes in your VPN service. However, the process of hacking a VPN is very complicated, not to mention time-consuming. So, before they can even steal data from you, it is likely that your VPN service provider has already rolled out patches for known vulnerabilities.
Also, there is nothing to be worried about as long as you select a trustworthy VPN service that comes with in-built leak protection and uses the strongest encryption technologies.
