
Spoofing is a type of cyber-attack that occurs when a scammer impersonates a trusted source to access important information or data from you or your device. Spoofing can occur through websites, messages, calls, emails, IP addresses, and servers.
Typically, the basic purpose of spoofing is to obtain personal data, steal money, circumvent network access controls, or spread malware through corrupted attachments or links. As with every type of communication on the web, scammers will use spoofing to steal your identity and resources. Spoofing is a common practice used by tactical hackers. Spoofing incidents occur more frequently on extended sales days, such as Amazon Prime Day, the Flipkart Big Billion Day, and the likes. Spoofing also occurs with senior citizens with limited knowledge of the latest technology and digital trends. These trends add to the customers’ panic. Therefore, it is important to identify yourself in the face of such attacks, identify them and protect yourself from such attacks.
Spoofing depends on the ability of a scammer to masquerade as someone or something. Some attackers hide their communications – emails or phone calls – to come from a trusted person or organization. With these types of spoofing attacks, scammers try to trick you into giving sensitive personal information.
Spoofing attacks can also occur on a more technical level through DNS or IP address spoofing. An IP Address is usually shared by a single device or a group of devices on a particular network. But if you wish to alter your IP Address, follow this link at (https://iprouterlogin.com/192-168-1-2/). You will happen to discover all the information needed to login and create your unique IP Address. Spoofing in network security includes spoofing a computer or network to bypass security by using a fake IP address.
Redirecting Internet traffic at the DNS (Domain Name System) level.
Simulated ARP (Address Resolution Protocol) data within a local access network (LAN).
How does IP spoofing work?
Spoofing relies on two components – the actual spoof, such as a fake email address or a website. There is also the social engineering aspect, which compels the victims to make a move. For example, scammers might send an email from a trusted senior colleague or supervisor requesting that you suddenly transfer some cash online with a convincing reason for the request. Scammers know what wires must be pulled for a victim to make their desired move – in this instance, sanctioning a fraudulent wire transfer – without a doubt.
The data communicated over the internet is broken into several packets; later, those packets are transmitted individually and put together at the end. Every packet has an IP, which is the acronym of Internet Protocol responsible for vital information. Also, it contains the origin IP address and the target IP address. IP address Spoofing is a mere act of forging the knowledge of the origin IP header. In the process, the hacker involved in spoofing uses tricks and techniques to change the origin address of the packet so that the device it is attacking believes that the address is from an official and trustable source. Once the hacker breaks into a computer network, it becomes straightforward to survey and prospect the hacker’s computer system, aiming to hack. Any person who has the aim of causing harm and destruction in an unknown computer network could opt for choosing IP Spoofing. Hackers who use IP Spoofing majorly use this type of cyber-attack to create massive and severe attacks.
An effective spoofing attack can have serious consequences – including stealing personal or company data, qualifying it for use in future attacks, spreading malware, obtaining denied network access, or bypassing access controls. For organizations, spoofing attacks can sometimes lead to ransomware attacks or harmful and costly information breaches.
You can be deceived in different ways:
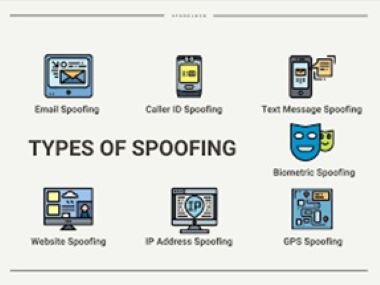
Spoofing can take many different forms and different types of attacks that you should look out for.
Below, we have listed some examples of different types of spoofing:
Caller ID spoofing
Caller ID (Caller ID) allows the receiver of a phone call to determine the caller’s identity. Caller ID spoofing occurs when a scammer/hacker uses falsified information and changes the caller ID. Since caller ID spoofing makes it impossible to block a number, many phone scammers use caller ID spoofing to hide their identities. Sometimes, these scammers will use your area code to show that the call is local.
Most caller ID spoofing occurs using a VoIP (Voice over Internet Protocol) method that allows scammers/spoofers to create a unique phone number and caller ID name of their choice. Once the call recipient on the other end answers the phone, the scammer will convince them to reveal important information.
Website spoofing
Website spoofing is when a scammer tries to make a dangerous website secure by using legitimate fonts, logos, background, and colors. Website Spoofing is done by replicating a trusted site to lead users to a phishing or malicious site. These copied sites will usually have the same website address as the original site and appear genuine at first glance. However, they are generally created to obtain the personal information of the visitor.
Email spoofing
Email spoofing occurs when a scammer sends spam emails with fake email addresses to infect your computer with malware, solicit money or steal your private information. These fake sender addresses are designed to make it look like they came from someone you know, such as a co-worker or friend.
These addresses can be made by either using alternate numbers or letters to make them look slightly different from the originals or by hiding the ‘From’ field to be the exact email address of someone already present in your network.
IP spoofing
When a scammer aims to hide where they are sending or requesting data online, they will typically use IP spoofing. IP spoofing tricks a computer into thinking that the information sent to the user is a trusted source and allows malicious content to pass through.
How to prevent IP Spoofing?
The ways to avoid and prevent computer networks from being the victim of IP Spoofing should be developed by experienced IT specialists.
- Regular monitoring of the networks to detect unusual activities is the most common way of preventing this cyber-attack. Establishing packet filters can also ascertain origin IP addresses that don’t tally with the IP address of the network in the organization. Packet filters are the most feasible way for the detection of IP Spoofing.
- Daily reminders to the team working in the organization and the employees to be aware of the emails they get in their inboxes. Any suspicious information that they come across should be immediately reported.
- Camps related to cyber awareness and education should constantly be held on the premises to educate more about cyber-crimes. Since the entire world is now working in the online mode due to the COVID-19 pandemic, it is more important to spread awareness about the malpractices that can tell someone’s entire business online. These camps will make the public aware of the cyber-crimes and make them well-informed about the security of their online portals, the importance of their passwords, and the details that are not to be shared with anyone who is unknown, or they are suspicious about.
- The computer networks should be built not to be left open without installing a quality check or control. Digital warnings and filters are critical in such a case. They would verify that the data is transmitted from the mentioned origin address and is not changed while on transmission.
- Deploying spoofing software on gadgets minimizes the risk associated with cyber-crime. Also, encrypted and authorized protocols in the computer network usually reduce the probability of completing a devastating IP Spoofing crime.
Being cautious about a dangerous act has no harm. So, if protecting the network from the beginning is managed well, the likelihood of being attacked is undoubtedly reduced. The network is also saved from IP Spoofing. Knowledge gained is never wasted; educating the employees to bear fruits for the company’s development and further benefit from being secured by cyber-crime is an achievement.
